The other day, I tried out Unroll.me, a clever new service that reads your inbox to let you unsubscribe from mailing lists and other unwanted e-mail flotsam with a single click.
As I was about to connect my Gmail account, my finger hovered over the “Grant access” button.
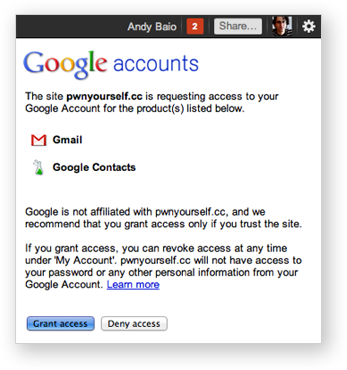
Wait a second. Who am I giving access to my Gmail account, anyway? There was no identifying information on their site — no company address, no team page listing the names of its team members, and broken links to their privacy policy or terms of service.
For all I knew, it could be run by unscrupulous spammers or an Anonymous troll looking for lulz. And I was about to give them unfettered access to eight years of my e-mail history and, with password resets, the ability to access any of my online accounts?
I had to dig around online to find out who’s behind it, and fortunately, Unroll.me is a totally legit NYC-based startup providing a useful service. I spoke to Perri Blake Gorman, Unroll.me’s cofounder and CMO, who assured me they’ll add all the company information as they roll out their public beta.
But since Gmail added OAuth support in March 2010, an increasing number of startups are asking for a perpetual, silent window into your inbox.
I’m concerned OAuth, while hugely convenient for both developers and users, may be paving the way for an inevitable privacy meltdown.
The Road to OAuth
For most of the last decade, alpha geeks railed against “the password anti-pattern,” the common practice for web apps to prompt for your password to a third-party, usually to scrape your e-mail address book to find friends on a social network. It was insecure and dangerous, effectively training users how to be phished.
The solution was OAuth, an open standard that lets you grant permission for one service to connect to another without ever exposing your username or password. Instead of passwords getting passed around, services are issued a token they can use to connect on your behalf.
If you’ve ever granted permission for a service to use your Twitter, Facebook, or Google account, you’ve used OAuth.
This was a radical improvement. It’s easier for users, taking a couple of clicks to authorize accounts, and passwords are never sent insecurely or stored by services who shouldn’t have them. And developers never have to worry about storing or transmitting private passwords.
But this convenience creates a new risk. It’s training people not to care.
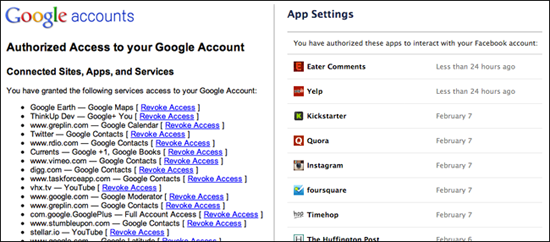
It’s so simple and pervasive that even savvy users have no issue letting dozens of new services access their various accounts.
I’m as guilty as anyone, with 49 apps connected to my Google account, 80 to Twitter, and over 120 connected to Facebook. Others are more extreme. My friend Sam is a developer at Kickstarter, and he authorized 148 apps to use his Twitter account. Anil counted 88 apps using his Google account, with nine granted access to Gmail.
For Twitter, the consequences are unlikely to be serious since almost all activity is public. For Facebook, a mass leak of private Facebook photos could certainly be embarrassing.
But for Gmail, I’m very concerned that it opens a major security flaw that’s begging to be exploited.
The Privacy Danger
A long list of services, large and small, request indefinite access to your Gmail account.
I asked on Twitter and Google+ for people to check their Google app permissions to see who they’ve granted Gmail access to. The list includes a range of inbox organizers, backup services, email utilities, and productivity apps: TripIt, Greplin, Rapportive, Xobni, Gist, OtherInbox, Unsubscribe, Backupify, Blippy, Threadsy, Nuevasync, How’s My Email, ToutApp, ifttt, Email Game, Boomerang, Kwaga, Mozilla F1, 0boxer, Taskforce, and Cloudmagic.
Once granted, all of these services are issued a token that gives unlimited access to your complete Gmail history. And that’s where the danger lies.
You may trust Google to keep your email safe, but do you trust a three-month-old Y Combinator-funded startup created by three college kids? Or a side project from an engineer working in his 20 percent time? How about a disgruntled or curious employee of one of these third-party services?
Any of these services becomes the weakest link to access the e-mail for thousands of users. If one’s hacked or the list of tokens leaked, everyone who ever used that service risks exposing his complete Gmail archive.
The scariest thing? If the third-party service doesn’t discover the hack or chooses not to invalidate its tokens, you may never know you’re exposed.
In the past, Gmail’s issued security warnings to accounts being accessed from multiple IP addresses. I spoke to OtherInbox founder Joshua Baer, and he said that Google’s eased up on the warnings because of the prevalence of third-party services.
It’s entirely possible for someone with a stolen token to read, search, and download all your mail to their server for months, and you’d never find out unless they exposed themselves, or you were diligently auditing your “Last account activity” history.
Stay Safe
Clearly, we’re not going to stop using awesome new utilities just because there’s a privacy risk. But there are best practices you can follow to stay safe.
- Clean up your app permissions. The best thing you could do, right now, is to log into each service you care about and revoke access to the apps you no longer use or care about, especially those that have access to Gmail. Finding the permissions pages can be tricky, but the nice folks at MyPermissions.org made a handy dashboard linking to every one.
- Think before you authorize. Before authorizing an account, find out who you’re granting access to. Look for a staff page, contact address, and take a look at the privacy policy to make sure they’re not sharing or selling your info with third parties. Bonus points if they outline their security policies and offer a way to disconnect service from within the app. If anything seems off, don’t do it.
- When in doubt, change your password. Have a feeling that someone might be reading your mail, but not sure which app is to blame? Changing your password instantly invalidates all your Google and Facebook OAuth tokens, though Twitter tokens persist after password changes.
Google could improve, as well. Their permissions page is too hard to find, even for experienced users, and it’s impossible to see which apps have accessed your account recently.
Facebook does an excellent job with this, but Google only shows you the IP address and the protocol it used to connect. Surfacing this information, as a periodic e-mail or on-site notification, would go a long way to averting a potential disaster.
The Greatest Troll of All
So, I originally published everything above over on my Wired column yesterday, but I left off something else I’ve been thinking about.

While I think a compromised database is the most likely scenario, there’s another possibility that disturbs me more.
Imagine that a brand new service pops up, offering a simple, fun service that uses your Gmail account. Maybe a neat visualization like Tout’s Year in Review, or maybe something more practical like sending all your attachments to Dropbox.
But it’s all just a giant troll, where the app’s creators are silently running targeted searches, downloading your mail, and looking for compromising photos and sensitive documents behind-the-scenes. They could collect the documents for months or years, and then release it all online in an anonymous blast. Lulz!
You’d likely never find out where the data came from, and the perpetrators would never be caught. Hell, if you’ve Gmail-authed a questionable app, this could be happening to you right now and you’d never know. Whee!

What else could be a bigger solution here?
Maybe special API interfaces to email that would allow for more limited levels of access (though that has other problems)?
Somewhat tighter control of who can create such an app on behalf of Google?
Limits to what IPs are used to poll this data? (This is a performance issue too, but may make it easier to detect unusual behavior)
IMO, when Unroll Me tells a user “Beta access denied!” then they should automatically revoke their own access to his/her gmail. I’ll trust they aren’t trolls but they shouldn’t need me to grant access to my gmail and then tell me it is beta and can’t use their service yet.
In your screenshot, none of those apps seem to have access to your mail, just to other google products. So, for the sake of clarity (for unsavvy but paranoid readers like me): does granting access to *any* google account service also grant access to gmail?
Serious questions, so forgive my bluntness:
1) You really allowed a third party site to access your real, main, serious, actually-use-it-for-things-to-do-with-your-identity email?
2) Are you the sort of person anyone should listen to regarding email security?
I get worried enough about this sort of exposure when I use a IMAP client, even though the behaviour of those applications with respect to data theft can be somewhat monitored by a firewall.
Your only advice for users should be to never allow OAuth access for their primary gmail account. Checking their site to see if they seem legit is a nonsense.
Play with these apps all you like on separate Google accounts.
If you need an oAuth app to really have access to emails that come to your primary account, forward them by rule to a different google account and grant access to that. This limits your exposure to the admittedly theoretical risk that an oAuth loophole could cause you to lose access to an account.
This is an alarmist and badly written article.
OAuth2 gives “scopes” which you, as developers, ask for. Most of the examples you give have not asked for the Gmail “scope” – including my own website, Media UK (which asks for no such thing). Media UK asks for “Gmail+ You, and Profile Information”. We have no access to your Gmail account nor your contacts. We know who you are (profile), what you look like (G+), and that’s it.
This isn’t an issue with OAuth: this is an issue with people who blindly click through requests that ask for ridiculous privileges like “can I look through all your Gmail?” OAuth2 is finely-grained and gives people exact control about what information they give. Don’t shoot OAuth. Shoot either Google’s UX, or the users themselves.
James: I’m not bashing OAuth. Like I said repeatedly in my article, it’s a radical improvement over sharing passwords for users, developers, and service providers.
OAuth does allow scoping, but Gmail doesn’t support them. It’s all-or-nothing access, which is the crux of my article. I’m concerned by the rising trend of apps asking for this access, and that people don’t realize how much power they’re giving unknown startups. It’s alarmist because I want to raise alarms. I’m trying to raise awareness to the issue.
As for your app, it doesn’t request Gmail access at all. As you can see in this screenshot, it requests “Google+ You” access, not “Gmail+ You” like you stated.
I’m not concerned about apps like yours that only use Google for signin or finding contacts.
Maybe I’m just a fucking idiot, but when Andy says:
“But this convenience creates a new risk. It’s training people not to care.”
He is indeed putting the blame on Google’s UX and the users, not shooting OAUTH.
josh: No, the only apps that have access to your mail are those that explicitly say “Gmail” next to them. There are none in my screenshot because I don’t authorize any apps to read my mail.
Michael: No, I don’t. But millions of people do, which is why I wrote this article. OtherInbox alone has over a million users.
One note, a per-user OAuth token isn’t useful without the per-client secret key as well. Both are needed to make a valid request. This is to help mitigate the first attack you mentioned, where the per-user tokens are exposed by a database compromise.
If both the client secret and the tokens are compromised, an attacker can impersonate that particular client — but at least then it’s later possible to determine which client leaked the tokens (because it’s their secret being used).
Great point. Thanks, John!
I don’t quite understand the tone of this article. I agree with Michael: The only advice should be “Never grant anything access to your email account.” In the comments, you said that you personally never do grant access to your email. But that’s not at all clear from the main text. In fact, you’ve sort of suggested the opposite. You say you tried out Unroll.me, and don’t mention that it wasn’t on your real account. You say you were worried (which strongly suggests that it was on an account that matters), but that you then found out it was run by a “totally legit” random startup providing a “useful service” (which I guess you’d never personally use, but again you’re suggesting the opposite here) and talked to the cofounder. And I guess you granted it access then.
I might be totally confused about something here. But I’m wondering why your first and only reaction to Unroll.me wasn’t something like this: “There is no good reason to ever grant anyone unfettered access to my email account. I should write an article explains to everybody why that’s true, and why, no matter how useful services like Unroll.me seem to be, they’re ultimately not worth the risk.”
Dustin: I’ve used these services, but I don’t leave that access open. I’ve tried apps like Greplin, FindBigMail and ToutApp, but I always revoke access after I’m done.
You’re right, the safest bet it to never grant access to any external app.
But I don’t think a message of complete abstinence is realistic for the millions of users that use inbox organizers and backup services, and find them invaluable, so I was just trying to raise awareness of the potential risks.
Hi Andy,
Could you clarify for me if granting authorisation to any app in Google means they can automatically READ all my emails in Gmail.
I wouldn’t think Google will give any app that level of access that this article seems to apply.
Can you please shed more light on what exactly an app can access when you give it access to your Google account and how you mean it can read all emails, download pics in emails, etc.
The only apps on your app permissions page that can read your email are the ones that specifically say “Gmail” or “Full Account Access.” Apps that can access your Google Contacts, or “Sign-in with your Google account” can’t access your mail.
Fair enough! I’m pretty paranoid about authorizing stuff like this, so I don’t have a very good perspective. But that makes sense.
I took a business law class and asked my (specialty: contract law) instructor “OK so when you need to rent a car, do you read every single line of that contract?”
He said no. I asked why not and he said because no matter what it says he’d rent the car anyway.
I have been doing some reading on legal precedents surrounding click-thru contracts and terms of service. They are binding (thus far).
So whether you are talking about an app developer or a website, a legitimate company or an intentional scam, the fact is these things are often intentionally written to be intelligible, not to mention prohibitively long, and there is just no way to know, care, understand or assert privacy online. And that is an acceptable practice and the real crux of the issue, IMHO.
What a gift idea for all Murdoch’s minions or other snoops, who want to get “some human interest” post hackgate. Maybe this idea should be forwarded to Leveson, in case he wants to add some extra recommendations to cover it.
It’s well after you wrote this, but on the off chance that you still get comment notifications: I’m wondering when we will hear about an oAuth-driven phishing attack.
Google does not is help you understand who the apps that have permission are. All they give you is the name of the app. When I reviewed the 32 apps that had access to my gmail (of the 66 that had access to any part of my Google account), I found a couple that I vaguely recall authorizing but can no longer recall what they do, like Yet Another Mail Merge and Autobot. More alarmingly I found one called “anonymous” (I revoked that one fast).
FB by comparison gives you the logo as a quick memory trigger, as well as links to their privacy policy and ToS, to at least give you some chance to verify that the app is indeed who they say it is.
Now i’m very happy that I stumbled upon this while in my look for something concerning this.